Introduction to biometrics
When you want to prove that you are who you claim you are, you rely on
- Something you know: PIN, password...
- Something you have: key, token, card...
But does not insure that you are here and the real owner. Biometrics relies on:
- Something you are: a biometric.
Well, you will find this (simple) "3-tiers" model very often in presentations, even by well-known people in this area. In general, the reaction is "Oh! Nice model, I understand that and make it mine immediatly".
Unfortunately, this is not enough. Think a little about this:
- Would you perform a transaction with a person in coma? or simply asleep?
I don't think so...
- You know: does not work
- You have: does not work
- You are: looks better, but no, does not work.
- You do: this is the good one. See further in the security section.
Now, you know the good question to ask to an annoying pretentious guy who knows everything about biometrics.
Definition
Biometrics: the automated recognition of individuals based on their biological and behavioral characteristics.
A basic system
Here is a simple fingerprint recognition system.
The first step consists in reading then recording a fingerprint on a smart card.
During the second step, a new fingerprint is read, then compared to the recorded fingerprint.

The fundamental principle of biometrics
There is only diagram to know. If you remember it, then you will be good at explaining biometrics...
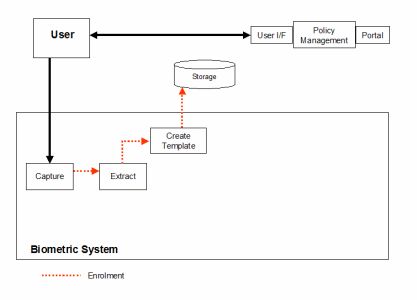
Enrollment
The first step in any biometric system is called enrollment. This is where one or several samples of the biometric to be used is ''captured" i.e. sensed by the capture mechanism. These samples are then passed to a processing mechanism, either a computer, or some type of embedded processor, which extracts the unique features of the sample to create a template, a mathematical or visual representation of the sample which takes up much less space than the original sample and which typically cannot be turned back into the original biometric. This template is then stored in some type of medium, whether it be on a magnetic stripe on the back of a card, or a computer's hard disk, or in a memory chip.
Authenticate / Identify
When a previously enrolled user decides to gain access to data or a facility via a biometric system, the user would present his biometric to the capture mechanism once again. The processing system would then do one or two actions, depending on the requirements of the application. If the processing system were only checking the live biometric against a single stored template, the system would be performing verification, wherein a one-to-one match is being done (authentication). If, however, the system were comparing this live biometric to a database of several previously stored templates, (most of which are not the users), the system would then be performing identification, searching through each template to see if it matches with the live biometric. This method is also known as a one-to-few or one-to-many search (identification). If, in either situation, a match was made, the person is granted access. If however, no match is made, the system denies access.
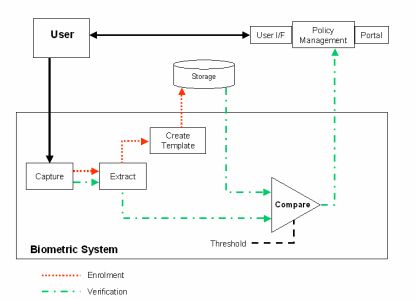
Once again, this schematic looks good, but there is something missing when it comes to security.
Accuracy
It is important to note that biometric identification works on the principle of a threshold. That is, it is nearly impossible to capture the biometric the same way every time it is used for access. Therefore, the system cannot expect a 100% match. Instead, a thresholding system is used that can be modified depending on the application.
For very secure applications, where we can allow false rejections due to the level of security, the threshold would be set very high, so that only those live biometrics which matched, say, 99% of the template would be allowed in. In low security applications, though, we may be able to deal with a few false acceptances because whatever is being protected is of low value or may be protected by other means as well. In this case, the threshold may be set to 70%.
Desirable qualities of biometric features
- Robust
- Stable and repeatable, time-invariant
- Difficult to spoof
- Distinctive: "Unique" amongst a population
- Accessible - easy to use
- Acceptable - non-intrusive